Unlock the potential of Open Finance
Connect your product to your users’ financial data easily and securely through a single platform. Access a variety of data sources including Open Banking to build engaging experiences your users will love.
- Questions?
- Contact our sales team
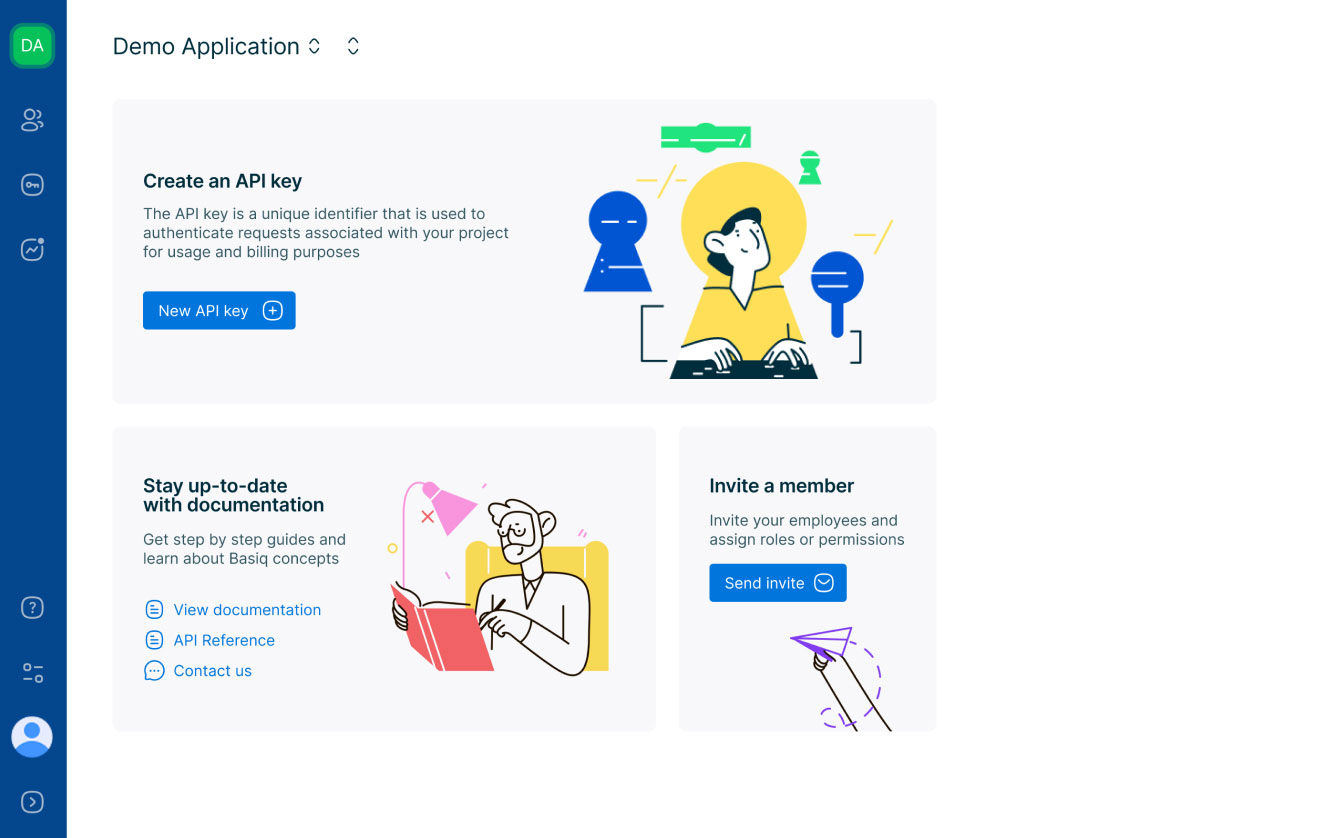
One platform to rule them all
All the tools you need to build your application
-
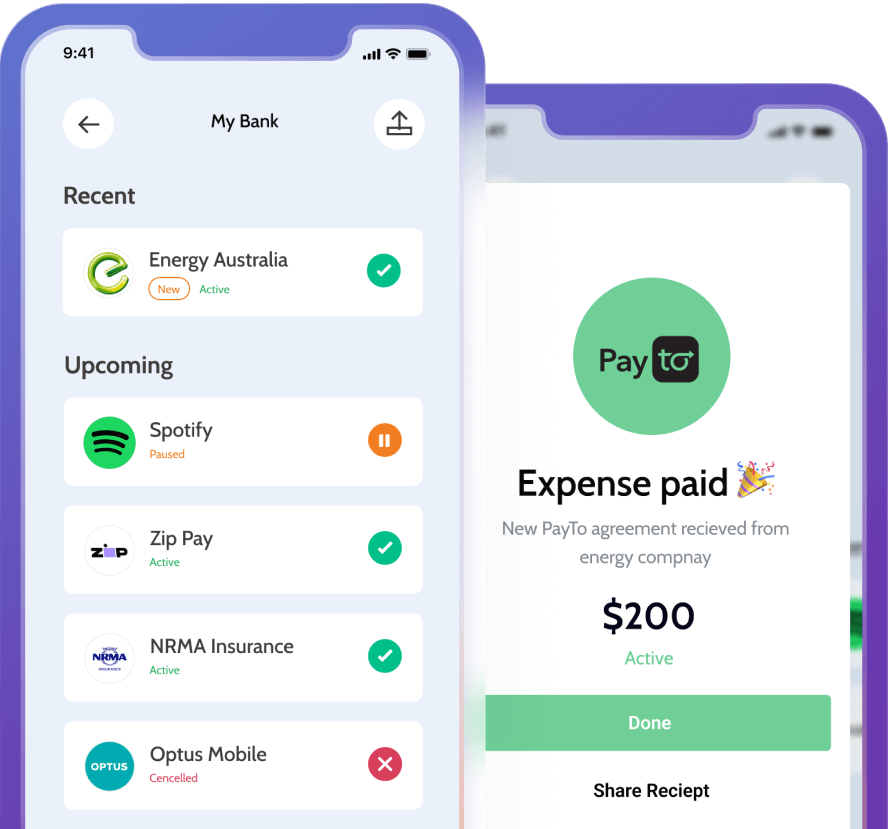
Data
Get access to data from banks, other financial institutions including superannuation & energy providers. With access to information including accounts and transactions through Open Banking, get the most complete picture of end users to launch your application.
Learn moreTransactions
-

Hungry Jack’s
-

Deliveroo
-

Income from Apollo Group
-

BP Fuel
-

Uber
-
-
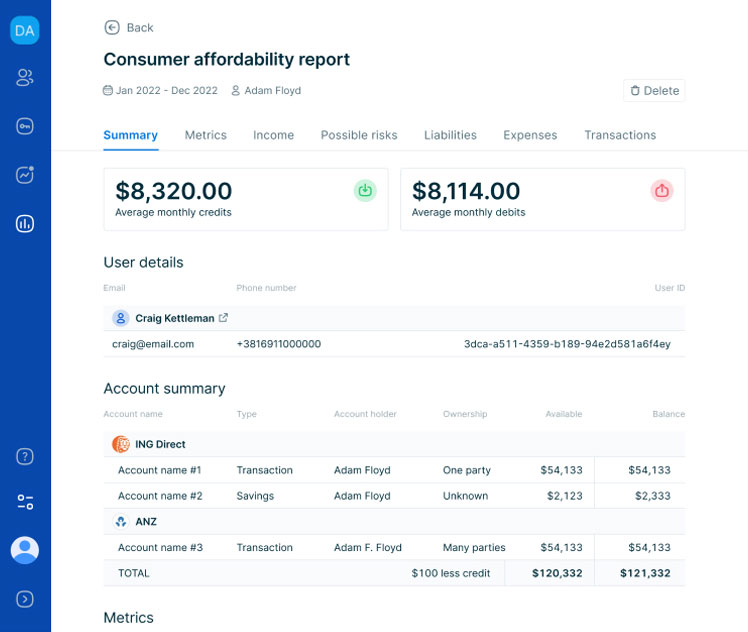
Insights
Identify specific patterns and trends from financial data such as income, expenses, assets and liabilities. Generate affordability insights to get a comprehensive view of end users.
Learn moreSummary
Metrics
-
-
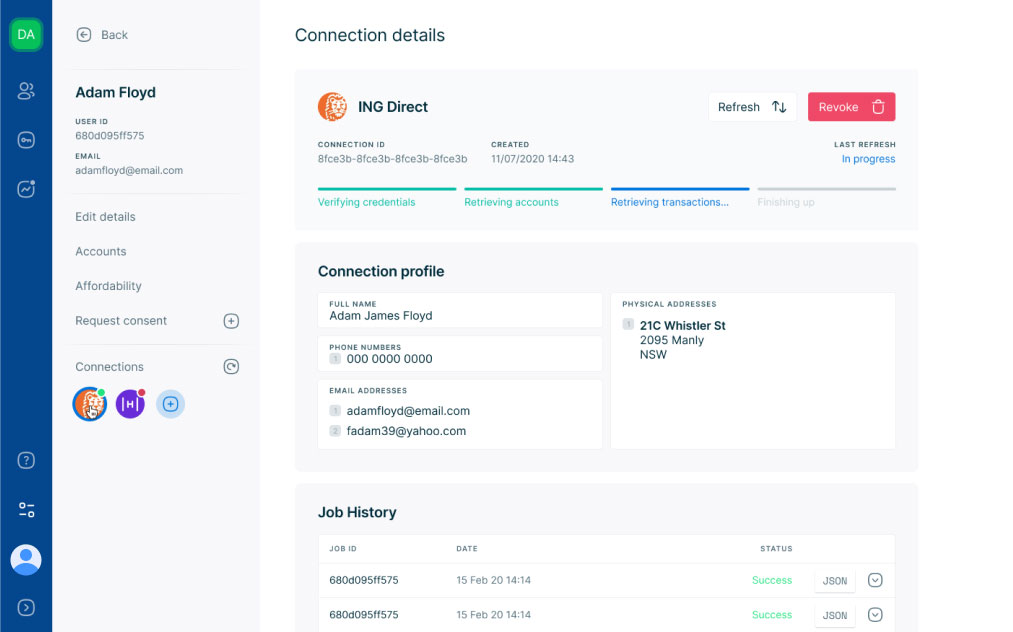
Data holder
Meet requirements of the CDR with a comprehensive data holder solution encompassing authorisation, compliance, consent management, security and ongoing reporting.
Learn more
Australia’s leading Open Banking platform
If you’re looking to get access to Open Banking, we’ve got you covered. Basiq provides all the knowledge and tools you need to access and use Open Banking data. Learn more at Basiq’s Open Banking hub.
Consumers
have shared their data through the
Basiq platform
Organisations
have accessed data through the
Basiq platform
Data Sources
covering all major institutions with access
to 99% of the AU & NZ population
Explore Use Cases

Developer Friendly Open Banking APIs
Built for developers
Get a head start with our developer guides, and make your first call to our APIs within a few minutes. Simple to use, RESTful, and fully documented APIs that help you integrate seamlessly with your application. Our intuitive sandbox allows you to test your apps before going live.
Get started
{
curl --request GET \
--url
https://au-api.basiq.io/users/d65a5499-cbc7-49b7-9f47-d30ea367ee13/accounts/465a5499-cbc7-49b7-9f47-d32ea367ee13
\
--header 'accept:
application/json' \
--header
'authorization: Bearer {token}'
Submit >
{
"type": "account",
"id":
"s55bf3",
"accountHolder": "GAVIN
BELSON",
"accountNo":
"600000-157441965",
"availableFunds":
"420.28",
"balance":
"356.50",
"creditLimit":
"400000.00",
"class": {
"type":
"mortgage",
"product": "Hooli Home
Loan"
},
"connection":
"8fce3b",
"currency": "AUD",
"institution":
"AU00000",
"lastUpdated":
"2019-09-28T13:39:33Z",
"name": "Master
Savings",
"status":
"available",
"transactionIntervals": [
{
"from": "2018-07-01",
"to": "2018-12-30"
}
],
"links": {
"institution":
"https://au-api.basiq.io/institutions/AU00000",
"transactions":
"https://au-api.basiq.io/users/ea3a81/transactions?filter=account.id.eq('s55bf3')",
"self":
"https://au-api.basiq.io/users/cd6fbd92/accounts/319ae910"
}

Developer quick start guides
Everything you need to successfully integrate with the Basiq API
Read docs
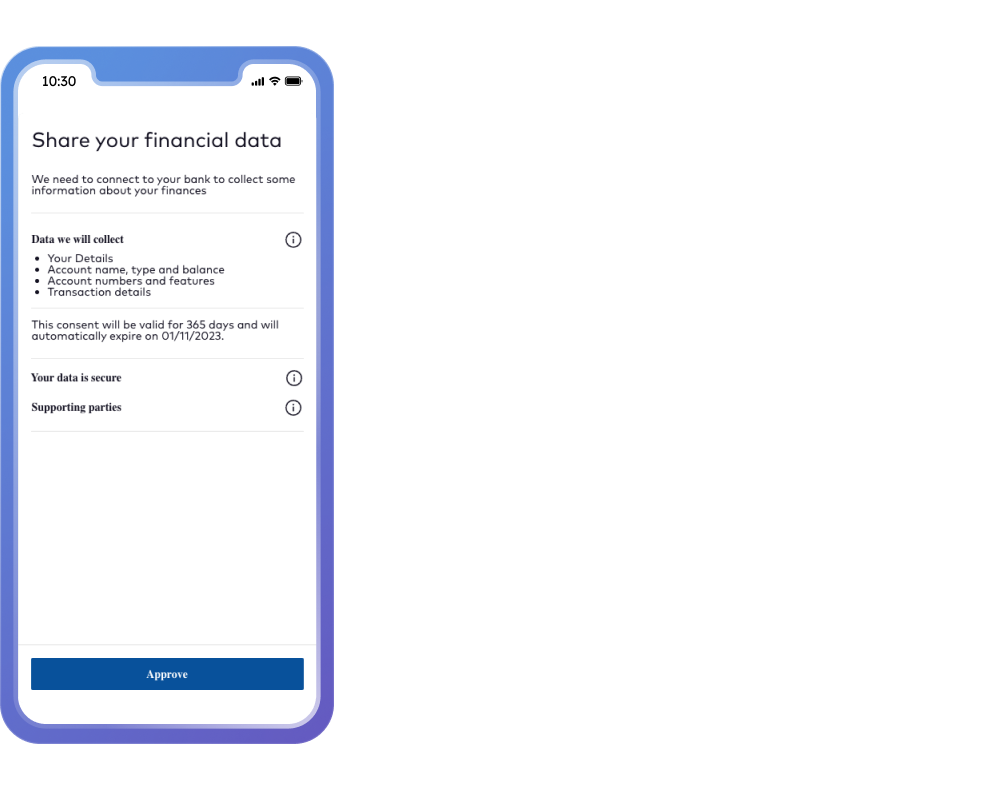
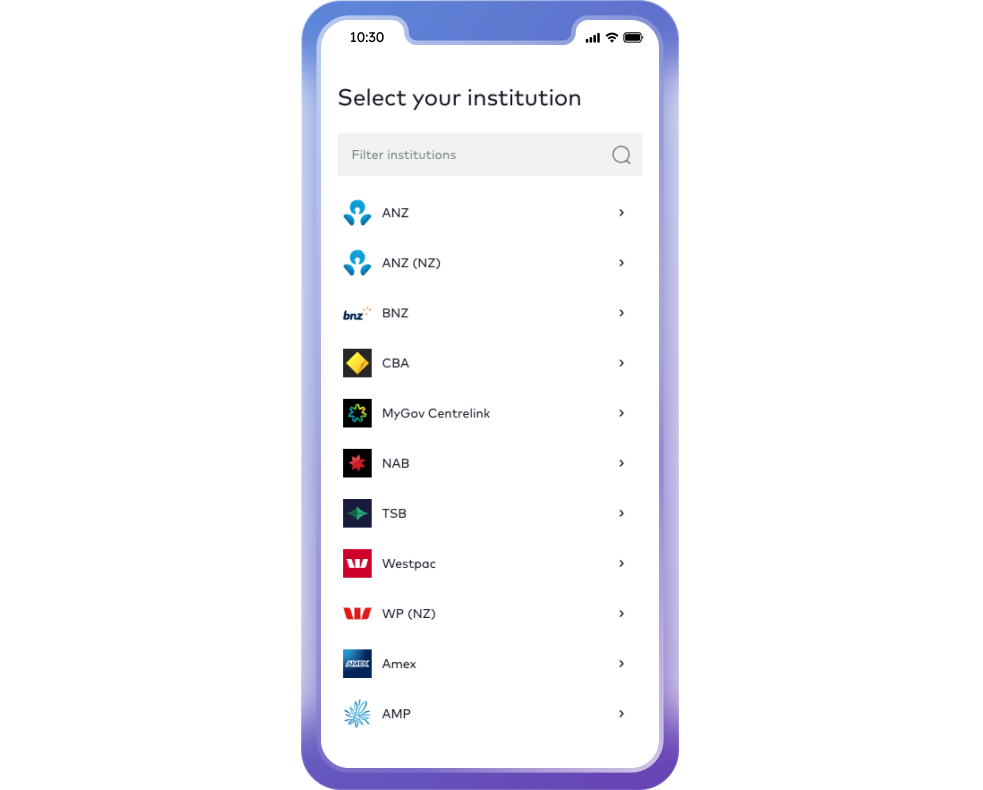
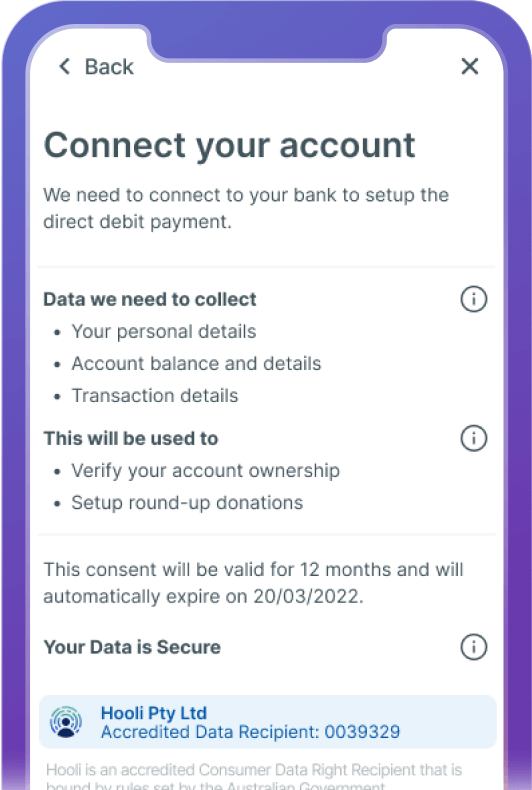
Easy to use consent solution
Reduce development costs and accelerate time to market with an out of the box consent UI. Create a more native experience and easily integrate into your application.
-
Define data scope and purpose of collection
-
Manage consent policies and dynamically generate the UI
-
Configure branding, styling & content elements
-
Integrate analytics to optimise user journeys
-
Preview changes in editor before going live
Ready to get started with Basiq?
Get in touch with one of our team members or create an account